PowerCLI is one of the more popular scripting environments for VMware administrators and architects around the world, with good reason. It’s also something that newcomers to VMware environments often shy away from when errors are encountered.
Hoping to save you some time and a few clicks by sharing the most common first error that admins may bump into. Many VMware vCenter environments are using self-signed TLS (aka SSL) certificates. This is very common, especially with home labs.
My PowerCLI Won’t Connect to vCenter!!
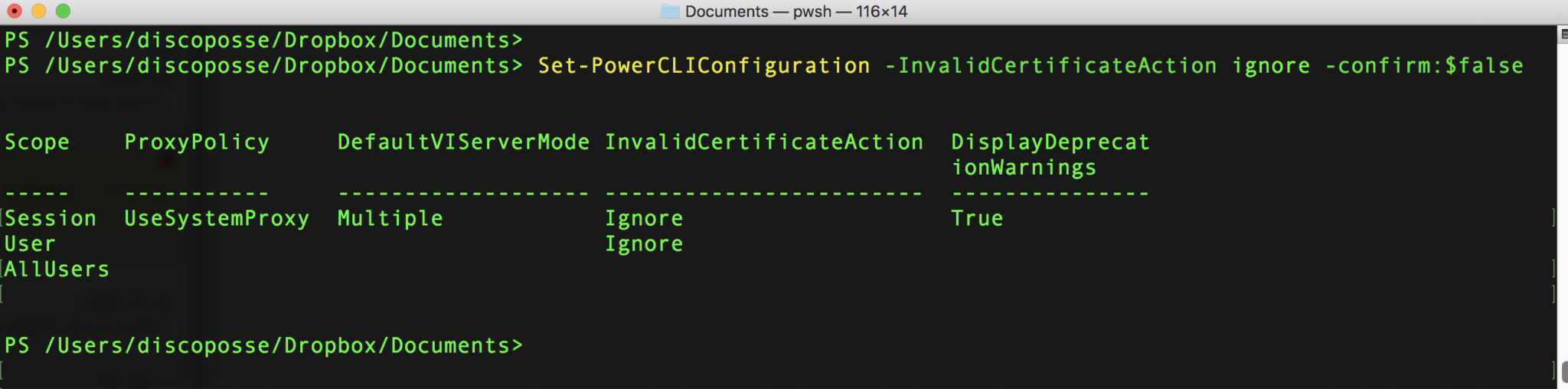
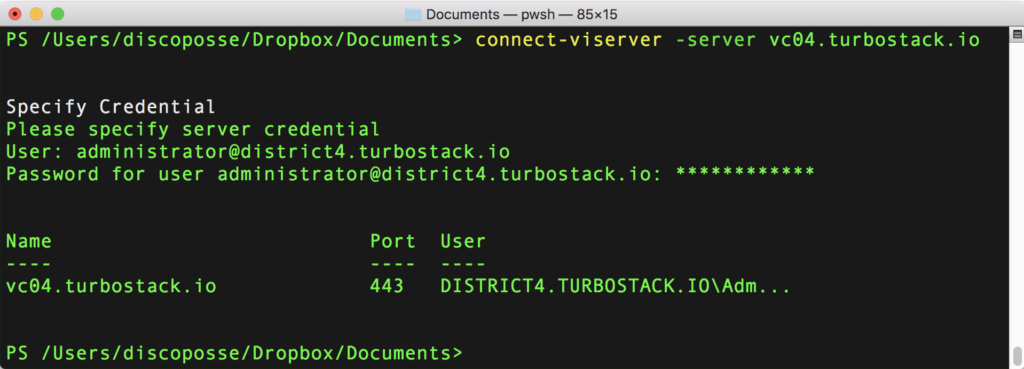
The default configuration for PowerCLI is to require the use of a secure channel and to verify the certificate chain. When first connecting to your vCenter without a certificate, or with a self-signed certificate, the command is super simple:
Connect-VIServer -Server YOURSERVERFQDN
Here is what happens:
The clear error condition shows that states “Could not establish trust relationship for the SSL/TLS secure channel with authority” for the FQDN (Fully Qualified Domain Name) of my vCenter server.
There is a simple fix for this. The caveat with this fix is that you must be aware that you are enabling connections from PowerCLI to unsigned certificates. As long as you are able to trust the target environments, this setting should be agreeable. It must be noted just for the sake of proper security practices which should require the use of publicly signed or internally signed and validated TLS certificates.
Fixing TLS Errors for PowerCLI with the Ignore InvalidCertificateAction option
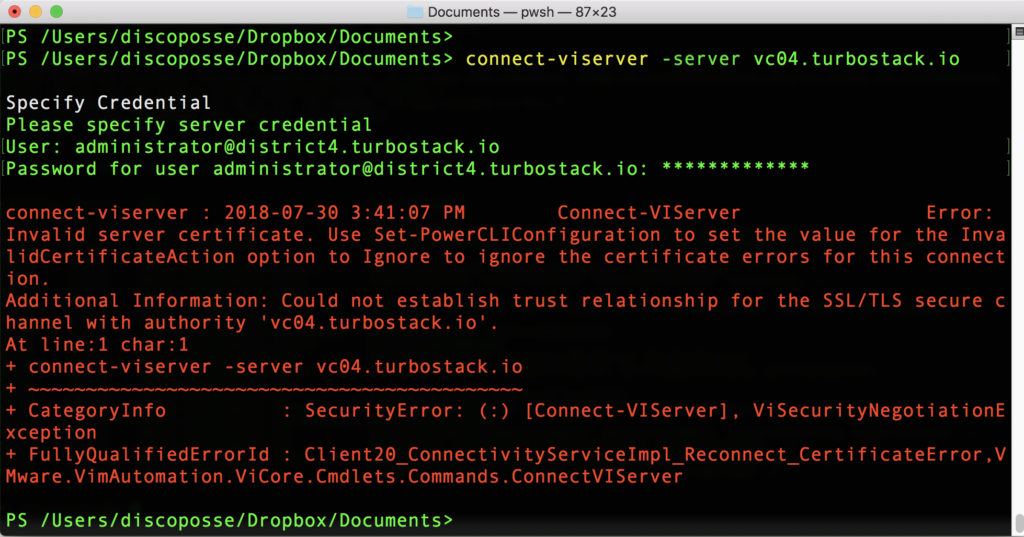
The configuration that needs to be set is the InvalidCertificateAction parameter. When set to the default it will deny access. The parameter must be changed by setting InvalidCertificateAction to Ignore which does not do a certificate check before performing actions using TLS.
The command is as follows:
Set-PowerCLIConfiguration -InvalidCertificateAction Ignore -confirm:$false
The resulting table shows the new parameter set as Ignore and now the Connect-VIServer will succeed even with our self-signed or invalid TLS certificate in place:
Hopefully this saves you some difficulty if the issue has stopped your PowerCLI from working as expected.